According to Pindrop Security, one in every 2,500 calls is a fraud attempt. Call center fraud is on the rise, especially with the increased use of IP-telephony, making it cheap and easy for scammers to make illegal calls from anywhere around the world. Fraudsters augment publically available identity information by repeatedly calling call centers and individuals to get one more piece of information. Before long, the army of callers has pieced together enough information to be able to access bank accounts and credit cards. But if they call the contact center from an unknown or unusual phone number, they are subject to heightened security measures which they typically cannot pass. If however, the call appears to come from the account holder’s phone, they are subject to a lower level security test, which they can pass, and this is where ANI-spoofing comes into play. Fraudsters with a minimal level of telephony knowledge can spoof the ANI, which stands for Automatic Number Identification and proxies for the phone number of the dialing party. In fact, ANI tells the phone company how to calculate call billing, but organizations rely on this value, which is passed through telephony networks, to assist in identifying the caller. So spoofing ANI, is an important part of perpetrating call center fraud.
The authentication challenge
Authentication of callers can be challenging for both the business and the consumer. Often the consumer doesn’t have the necessary account info or may have forgotten their PIN (shocker) or security questions, making it hard to verify their identity and providing the service they need. Each layer of authentication that is added to the system only serves to erode the caller experience, decrease loyalty, and make it far more difficult and time consuming for agents. By identifying increased (or reduced) fraud risk in advance, companies can focus their authentication efforts where they are needed and where they can make an important difference. Being able to identify calls where the ANI was spoofed allow these questionable calls to be delivered to specialized agents trained to stop fraudsters before they get access to customer accounts.
How to identify fraudulent calls by fraud scoring with SIP-T
Accurately identifying fraudulent calls can be done utilizing signaling data that traverses networks with calls. There is a vast amount of signaling information facilitating calling in the PSTN (Public Switched Telephone Network) used to setup and teardown telephone calls, perform number translation, local number portability, prepaid billing, short message service (SMS), and other mass market services.
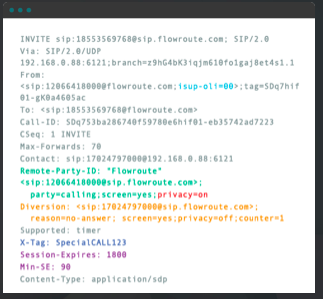
A portion of that signaling information is the ISUP (ISDN User Part) signaling which is used to set-up each phone call on the PSTN and contains useful metadata such as the circuit identification code (which can identify where the voice part of the call is carried), the called number, the type of interaction and the ANI. The ANI value can be changed, but when it is, it leaves behind other information incongruous with the new value, which are the tell tale signs of spoofing.
The big problem here is that most of this call data is lost when calls are passed between most carriers and further degraded when calls leave the PSTN over SIP. There is, however, a way to get this information back. Session Initiation Protocol for Telephones, or SIP-T for short, allows the encapsulation of additional telephone network-specific call information on the normal SIP signaling layer. By utilizing SIP-T, it is possible to implement fraud scoring and identify which calls are potentially fraudulent, allowing them to be dealt with accordingly.
OLI- Originating Line Information. Shows the type of line placing call.
JIP- Jurisdiction Information Parameter. Indicates geographic location of caller/switch.
CPN- Calling Party Number. NPAC dip will show true line type and native geographic switch. Compare with OLI and JIP.
FCI- Forward Call Indicator. Indicate domestic or international origin of call.
ANI- Charge Number. Discrepancy from CPN may indicate spoofed caller-ID.
Diversion- Forwarding is a tactic to forge switch origination information. Multiple diversions increase likelihood of fraud.
Example call flow with fraud scoring
- 1. First the calling party dials call center number. Validity of call info is unknown.
- 2. SIP-T pulled from SIP INVITE and NPAC data for calling party number pulled
- 3. Fraud logic compares authoritative data against call metadata and generates a fraud score
- 4. Switch routes call based on fraud score to appropriate end point
- 5. Trusted calls can be handled confidently, improving caller experience
- 6. Questionable calls can be investigated with fewer resources
Innovate with Telecom
Flowroute is focused on enabling our customers to innovate through leveraging unobstructed access to the PSTN. Enabling our customers to utilize fraud scoring is one of many creative applications which depend on open, real-time access to, and control of, telephony and messaging services. Fraud-scoring calls by leveraging advanced telecom signalling information has the potential of saving companies billions of dollars in fraud losses. This is a straight-forward but advanced innovation in telecom that a good developer, working with the right carrier, can implement and deliver tremendous value.